Cyber Crime and Cyber Attacks
Technology is almost in every aspect of our lives in the modern world. We cannot do without computers, networks, and the internet to operate the banking sector, education included. The resulting dependence also creates the possibility of cyber crime like cyber attacks, which may jeopardize our information and operations. To be safe on the Internet, it is critical to know what a cyber attack is and its numerous manifestations along with the connection to cyber crime and phishing.
What is Cyber Attack? Understanding
What is a cyber attack? It is simply a cyber crime and an act of individuals or groups of people using a calculated effort to compromise the information systems, networks or equipment of a person, organization or government. The attackers tend to steal data or disrupt services or corrupt a reputation or finances. The motives are different: it can be financial interest, political ambitions, personal score to settle or ideological commitments.
The contemporary attacks are more advanced. They are able to strike any target such as the multinational companies as well as individuals using the internet. Cyber crime has become a reality and therefore cybersecurity awareness is an essential part of the professional and personal life.
Cyber Crime: The Greater Thing.
Cyber crime is crime committed by using a computer, network, or the internet. All cyber attacks are categorized under cyber crime although not all cyber crime is in the form of an intricate attack.
Examples of cyber crime are:
– Identity theft- stealing personal data to commit fraud and cyber crime.
– Financial frauds – unauthorized entry to bank accounts or credit cards is supposed to be a cyber crime
– Cyberbullying- bullying or intimidation over the internet also called cyber crime.
– Data breaches- illegal access to sensitive or confidential information.
There is a connection between cyberspaces and cyber crime, and that can be explained through a cyber attack as a means of effecting a cyber crime. An example of this is a cyber attack and a cyber crime of hacking into the database of a company and stealing credit card information.
What is Phishing and How It Contributes to Cyber Attacks.
One of the most widespread forms of cyber attack in cyber crime is phishing. It is a form of social engineering, in which attackers manipulate individuals into surrendering confidential information like passwords, account numbers or other personal identification data.
Phishing may be conducted in emails, text messages or counterfeit websites, which resemble a reputable bank, social media, or government organization. As an example, a phishing email message may inform you that your bank account is being reviewed and that you need to press a button to check the information. By entering your information, the attackers take it and use it to commit a financial crime, identity theft, or illegally log in to their accounts | Underwater Drone
Phishing is not only an issue of individuals. Advanced campaigns have also been used against large corporations and government agencies causing them to experience breaches of data, revenue loss, and reputational damage.
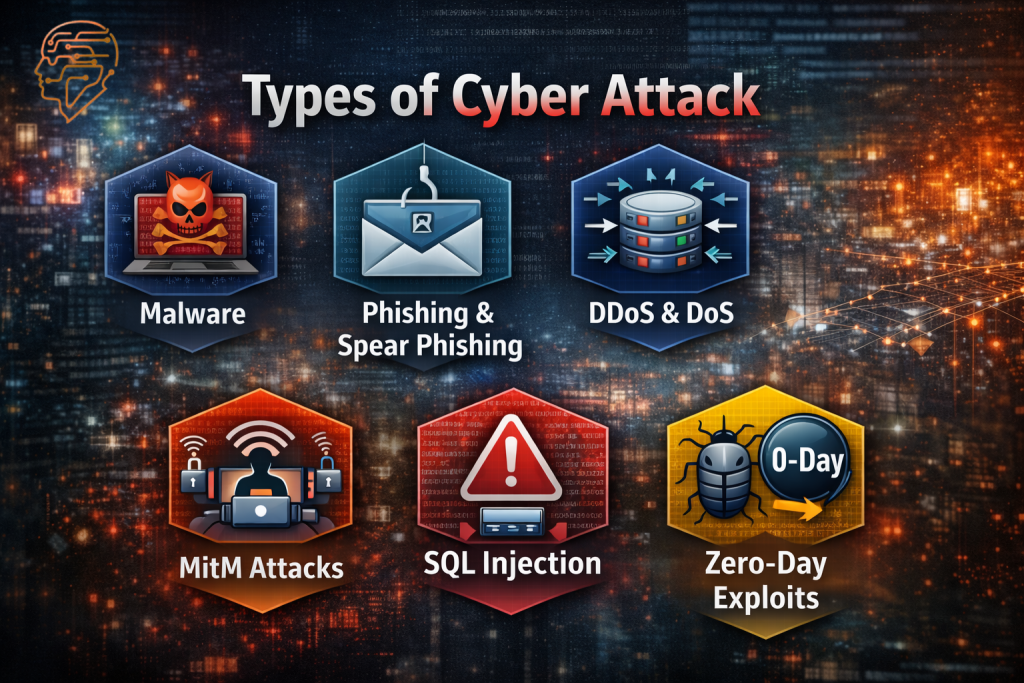
Types of Cyber Attack
As a way of safeguarding oneself and their organization, it is very important to understand the various forms of cyber attacks. Cyber attacks can be of different approaches, complexity, and effect. Here are the main categories:
Malware Attacks
Malicious software is abbreviated as malware. Such attacks leave software capable of destroying, disrupting or unlawfully attacking a computer system. Typical examples include:
- Viruses – programmes which may attach to the files and be transmitted to other systems.
- Worms– Malware that propagates automatically over the networks without user involvement.
- Trojan Horses– This is software which appears to be legitimate but is utilized to steal information.
- Ransomware – Viruses that encrypt files and demand any fees the files to be released.
Distributed Denial of Service (DDoS) and Denial of Service (DoS).
DoS and DDoS attacks are designed to render a system, a service and a network unusable to the system users. A DoS attack causes floods of traffic to a server or a network, achieving its resources. A DDoS attack involves more than one source in order to flood the target, resulting in more difficult mitigation. Such attacks are commonly employed to interfere with a business, launch hacktivist movements, or blackmail businesses.
Man-in-the-Middle (MitM) Attacks.
In a MitM attack, the attackers are able to intercept and potentially change communications between two parties without their awareness. It is possible on Wi-Fi networks that are unsecured, and hackers can intercept important information like logins or bank details.
SQL Injection Attacks
SQL injection is an attack on web applications, where malicious code is entered into the web application input fields, and the vulnerability of the website relies on database. The implication is that data can be read, edited, or deleted by attackers which can be a breach in most cases.
Zero-Day Exploits
A zero-day exploit is an attack in which the attackers exploit the vulnerability they have known of before the developer patches the vulnerability. The attacks in question are particularly harmful since there is no defense in place.
Password Attacks
Password attacks are brute-force, dictionary and credential stuffing attacks. Attackers attempt to get unauthorized access through the use of guessed or reused stolen passwords.
Phishing and Spear Phishing
One of the social-engineering attacks is phishing. Spear phishing attacks individual or organizations, which makes them more convincing and threatening.
Cyber Attacks in the real world.
To get a better picture of cyber attacks, it is useful to consider the following examples:

Jaguar Land Rover (JLR) Cyber Attack
In 2025, JLR suffered a cyber attack that affected its worldwide IT infrastructure and brought production to a stop in every part of the world incurring a loss. It demonstrates how the influence of an industry can be achieved.
WannaCry Ransomware -In the year 2017, WannaCry attacked hundreds of thousands of computers around the world, encrypting files and requiring ransom. The viruses used the unpatched Windows vulnerabilities and this illustrates the danger of outdated software.
Equifax Data Breach- In 2017, hackers accessed the system of the Equifax, which had major weaknesses, to access sensitive information of over 147 million individuals. This violation depicts the magnitude that can be caused by successful cyber attacks.
These examples demonstrate that it is not only individuals who are targeted in cyber attacks but corporations, governments and other critical infrastructure.
Preventing Cyber Attacks
However, though awareness of a cyber attack is key, prevention is also of essence. Some steps that can be made by organizations and individuals are:
Cyber Awareness and Training of the employees.
Employees are taught how to be cyber aware, how to be safe on browsing, and how to have safe password habits through cyber-awareness programs. Human error is one of the leading causes of attacks, which are minimized through training.
Powerful passwords and Multi-Factor Authentication (MFA).
Strong and distinct passwords and MFA can make it difficult to illegally gain entry. Attackers use weak or old passwords to access the system.
Periodical Software patches and updates.
Most cyber attacks take advantage of vulnerabilities of old software. Maintaining systems minimizes the threat of zero-day attacks and malware attacks.
Intrusion Detection, Firewalls and Antivirus.
Firewalls direct inbound and outbound network traffic. Antivirus programs identify programs that are malicious and intrusion detection systems monitor suspicious activity. All of these tools provide a digital defense barrier.
Backup and Disaster Recovery.
Periodically saving important data is beneficial in assisting organizations to retrieve their systems that were affected by ransomware or data-loss attacks.
Threat Intelligence and Monitoring.
Active surveillance of networks and threat intelligence enables the organization to identify attacks in their early stages in order to deal with them effectively.
Cybersecurity at the Personal Level.
Cyber attacks also are not a corporate issue only. People are usually victims of phishing, malware, and social engineering. To be safe, it is possible to remember some tips:
Always do not follow the unrecognized links or attachments.
Be sure that the sender is who he claims to be before providing sensitive information.
Apply anti-virus software and VPNs.
Updates of operating system and applications.
Research on typical cyber threats.

Future of Cyber Attacks
Attacks are becoming more advanced and common with the changing technology. Emerging trends include:
Attacks based on AI- Hackers rely on artificial intelligence to automated attacks or security bypass.
IoT vulnerabilities- smart home appliances and wearables are usually poorly secured and are the target.
Cloud security threats Cloud hackers take advantage of cloud configuration errors.
State-sponsored cyber attacks – countries are resorting more and more to cyber attacks in the form of spying, sabotage, or political pressure.
The nature of cyber attacks and the dynamic world of threats are important aspects that should be understood to safeguard the digital infrastructure.
Conclusion
In short, a cyber attack can be defined as any intentional action to harm the digital systems, networks, or data. These are closely connected to cyber crime and often include such tactics as phishing, and may be in a number of formats such as malware, ransomware, DoS attacks, and other forms of cyber crime.
It is important that both organizations and individuals should be aware of the kind of cyber attack, learn the actual cases, and take measures to prevent attacks. Cyber awareness, hygiene, and proactive defense are critical in the digital space as a safety, privacy and continuity in an era where technology is affecting every sphere of life.
The cyber attacks battle has not ended yet, and being informed is the initial step on how to protect yourself and your digital space.
Queries
1. What is a cyber attack?
A cyber attack is a deliberate attempt to damage or access computer systems, networks, or data for theft, disruption, or harm.
2. How is cyber crime related to cyber attacks?
Cyber attacks are methods used to commit cyber crime, such as data theft or fraud.
3. What is phishing in cyber crime and why is it dangerous?
Phishing tricks people into sharing sensitive info via fake emails or websites, leading to identity theft or financial loss.
4. What are the most common types of cyber attacks in cyber crime?
Common types include malware, ransomware, DoS/DDoS, MitM attacks, SQL injection, password attacks, and phishing.
5. How can ransomware affect individuals and organizations?
Ransomware locks files and demands payment, halting operations and risking data loss.
6. What is a zero-day exploit?
A zero-day exploit targets unknown software vulnerabilities before a patch is available.
7. How can individuals protect themselves from phishing attacks?
Avoid unknown links, verify senders, use strong passwords with MFA, update software, and use antivirus.
8. What was the Jaguar Land Rover (JLR) cyber attack?
In 2025, JLR’s IT systems were hacked, stopping global production and causing financial losses.
9. How is cyber awareness connected to preventing cyber attacks?
Cyber awareness educates people on safe online habits, reducing errors that lead to attacks.
10. What are the emerging cyber crime trends in cyber attacks?
Trends include AI-driven attacks, IoT vulnerabilities, cloud threats, and state-sponsored attacks.
